Underinvestment in Cybersecurity

In the last few decades IT systems have become a significant factor for every industry, increasing productivity, improving service offerings and increased the speed at which companies can deliver services. It is only right therefore that we ensure that these systems are not abused, damaged, or misused in a manner which can undermine the organisation […]
The Cost of a Breach

IBM’s 2024 Cost of a Data Breach report, identified that the average cost of a data breach in the UK reached £3.58 million, and that this cost had increased 5% since 2023. Verizon’s 2025 Data Breach Investigation report, suggested there was a 37% increase in ransomware attacks being reported, with a median payout of $115,000 […]
AI and Red Teaming

Red teaming is still fairly young as far as cybersecurity disciplines go – most of us in this part of the industry have come in from being penetration testing consultants, or have some sort of background in IT security with a good mix of coding and scripting skills to develop tools. Our work often requires […]
Data Hygiene

Most organisation’s that are breached and compromised are done so not because they are lax with security, have poor patching, or are gambling that they will never be a victim; instead they usually suffer from poor data hygiene. Users store data on desktops, in shared folders, in online repositories (such as Jira, SharePoint, Confluence, etc.), […]
DORA TLPT Guidance Update

Today the EU provided the long awaited updated guidance in relation to DORA’s TLPT: DORA TLPT Guidance Update This 30 page document further clarifies the necessity for Threat-Led Penetration Tests (TLPTs) under DORA. We will be posting a more in-depth post about this in the very near future, but the key points that should be […]
TIBER-BE Insights

The TIBER-EU framework is designed to help organisations improve their Cyber resiliency. It has multiple stages: initiation (scoping, procurement, planning), threat intelligence, penetration testing (red teaming), purple teaming (attack replays, additional untested control tests, variances in attack methodologies working alongside the Blue team), and closure (reporting, remediation plans, attestation). As a framework, TIBER can be […]
Cyber Threats & The Boardroom
In cybersecurity, the prevalent and growing threat from criminals is ransomware operations. This is where a threat actor manages to establish a foothold into an organisation, will try to position themselves to gain control of the organisation’s data, will often steal some or all of that data, and then encrypt as much of it as […]
Passwords
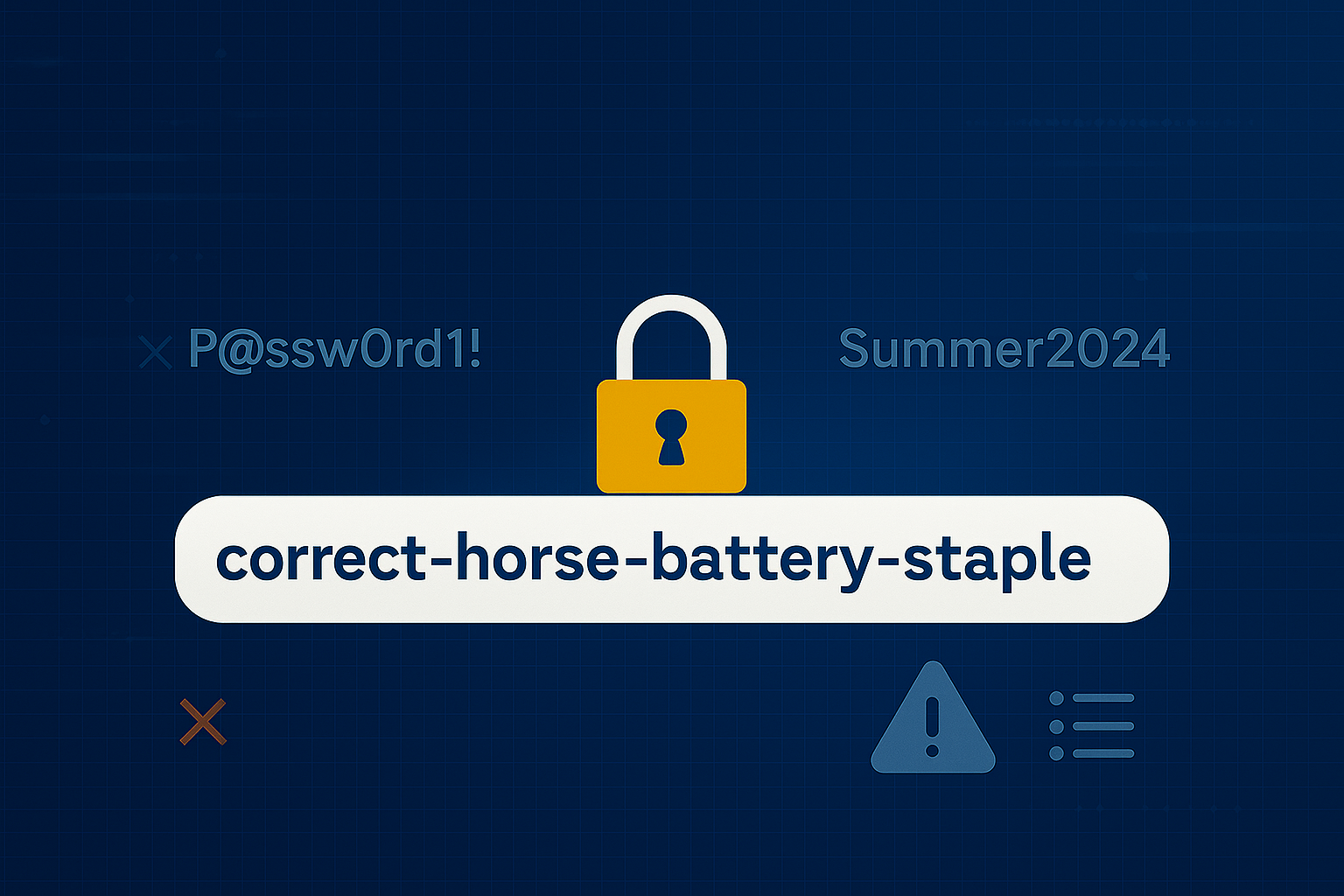
NIST, like the NCSC have updated their password guidance. It is now no longer advisable to set them to be random strings of nonsensical letters, numbers and symbols. The focus is now on password length, by stringing together multiple words. Inclusion of uppercase, and symbols or numbers is still helpful, to make them even harder […]
DORA

The Digital Operational Resilience Act (DORA), the EU regulation that came into force in January 2025, and affects financial entities and their suppliers mandates Threat-Led Penetration Testing (TLPT), alongside Risk Management for third parties, information sharing and incident reporting. The full impact of DORA’s requirements is still be absorbed by the industries it affects, and […]
The Quantum Spectre at the Banquet
Quantum is tipped to be the next big thing in computers, and it has been for some time – in fact it was first conceived in the 1980s; however the issue was not really considered until the mid-1990s. Now, it’s seen as a potential game changer in the world of cryptography, where the world’s secrets […]