Exploiting Mobile Apps Using Frida
This post explores how the Frida dynamic instrumentation toolkit can be used to bypass common mobile app security controls on both Android and iOS. Using real-world testing examples, it demonstrates how root detection, in-app scoring, and premium content restrictions can be manipulated when protections rely too heavily on client-side logic. The findings highlight the importance of enforcing access control and validation on the server to prevent exploitation.
Prism Infosec Partners With The UK Space Agency
Prism Infosec is delighted to announce a new partnership with the UK Space Agency, supporting the delivery of a national initiative to strengthen cybersecurity across the UK space industry. As part of this programme, Prism Infosec will work with small and medium-sized enterprises (SMEs) within the space sector to help them enhance their cybersecurity maturity […]
Announcing Our Rebrand: A New Era of Cyber Resilience

Today marks an exciting milestone for Prism Infosec – we are officially launching our rebrand. This rebrand is more than a fresh look. It represents our evolution as a cyber security partner and our commitment to helping organisations prepare for, respond to, and manage cyber risks with confidence. Why We Rebranded Cyber threats are evolving […]
UK Government Proposes Ban on Public Sector Ransomware Payments

On 22nd July 2025, the UK Government announced a significant legislative proposal aimed at reducing the incentive for ransomware attacks. Under the proposed law, public sector bodies and operators of Critical National Infrastructure (CNI) — including schools, local councils, the NHS, utilities, and data centres — would be prohibited from paying ransoms to cybercriminals. The […]
Why bother with Physical Breach Tests?

A physical red team (breach) test is a real-world simulation of a physical breach. Think: tailgating into a secure office, picking locks, planting rogue devices, or accessing server rooms without authorisation. Unlike standard security audits, red teamers think and act like real adversaries – covertly probing for the weakest link in physical security protocols, policies, […]
How We Got Here: A Brief Reflection on Cybersecurity’s Foundations

Computer technology as we know it, has existed for the merest blip of time in human history. In less than 90 years we have gone from valves and punchboards to pushing the boundaries of quantum states in an attempt to achieve computations that would take millions of years to achieve otherwise. We landed people on […]
Initial Access Brokers – The Gateway to Ransomware and Supply Chain Attacks

Initial Access Brokers (IABs) are part of the cybercrime-as-a-service ecosystem. They have become the first step in a number of high-profile compromises resulting in ransomware and supply-chain threats. These groups collect, package and sell credentials from a variety of sources for a variety of systems (such as VPN, RDP, SSH, etc), selling them with details […]
Abuses of AI
Much like Google and Anthropic, OpenAI have released their latest report on how threat actors are abusing AI for nefarious ends, such as using AI to scale deceptive recruitment efforts, or using AI to develop novel malware. It is no surprise that as AI has become more pervasive, cheap to gain access to, and readily […]
Initial Access Brokers – The Gateway to Ransomware and Supply Chain Attacks

Initial Access Brokers (IABs) are part of the cybercrime-as-a-service ecosystem. They have become the first step in a number of high-profile compromises resulting in ransomware and supply-chain threats. These groups collect, package and sell credentials from a variety of sources for a variety of systems (such as VPN, RDP, SSH, etc), selling them with details […]
Why Not Test in Dev?
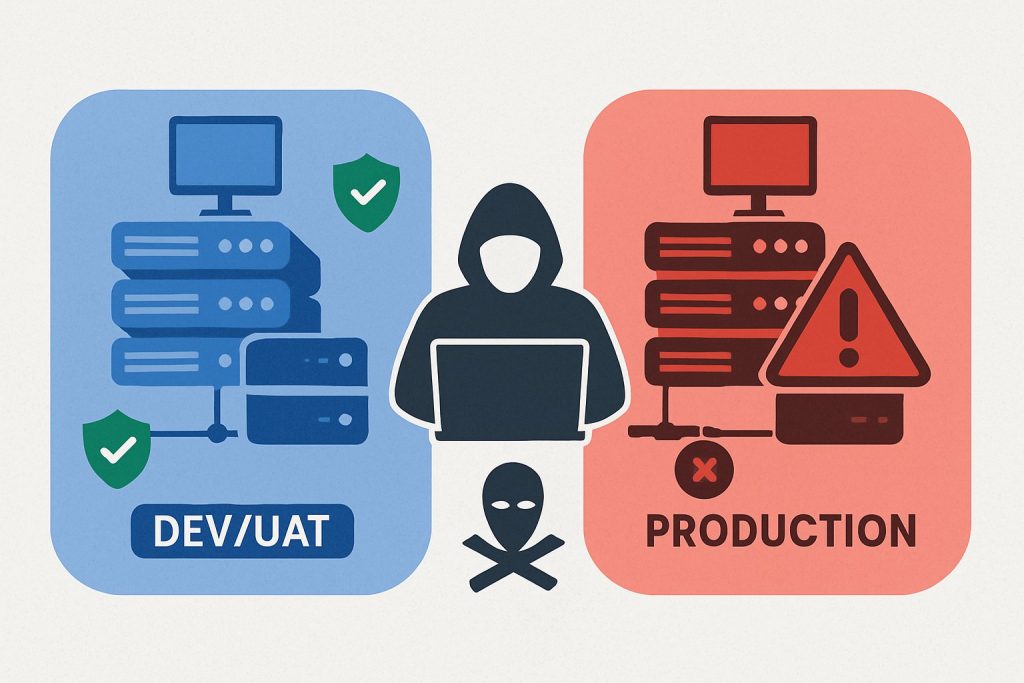
We frequently get asked by clients if we can do our red team tests in their DEV or UAT environments instead of production. We are told its identical to production – same systems, dummy but similar data, same security controls, same user accounts, etc. Etc. We get it, DEV and UAT environments are there to […]