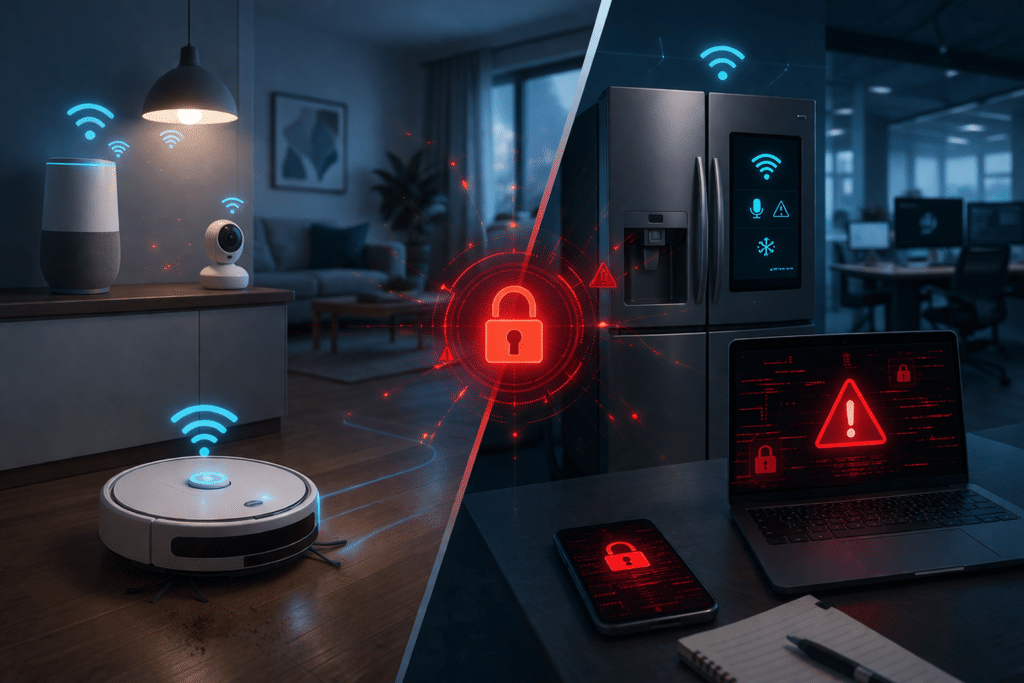
IOT or rather “connected devices” are now common in both homes and workplaces. From smart speakers and lighting systems to robot vacuum cleaners and internet-connected refrigerators, the number of Internet of Things (IoT) devices in use continues to grow rapidly.
Whilst these devices offer convenience and automation, they also introduce new security considerations.
Many consumer IoT devices are designed primarily with usability and cost in mind. As a result, security features may be limited, and software updates may not always be maintained throughout the product lifecycle.
Low-cost devices, high security exposure
Researchers have repeatedly identified vulnerabilities in consumer IoT devices including smart cameras, routers and home automation systems.
Issues often include:
- weak or hard-coded passwords
- unsecured APIs or communication channels
- outdated software components
- limited patching mechanisms
In some cases, adversaries have been able to gain remote access to devices or use them as entry points into wider networks.
Devices such as robot vacuum cleaners or smart kitchen appliances may appear harmless, but they often contain microphones, cameras or wireless connectivity that can expose sensitive data or network infrastructure.
The blurring boundary between IT and operational technology
As connected devices become more common in workplaces, the distinction between consumer technology and operational technology (OT) environments is becoming less clear.
Smart devices are increasingly used in offices, retail spaces and industrial environments for automation, monitoring or convenience.
If poorly secured devices connect to corporate networks, they can introduce unexpected attack paths that bypass traditional security controls.
Managing IoT security risk
Organisations should ensure that connected devices are treated as part of the broader technology estate rather than unmanaged consumer gadgets.
Security teams should consider:
- maintaining an inventory of connected devices
- segmenting IoT devices from critical systems – dedicated VLANs
- monitoring network activity associated with smart devices
- evaluating device security before deployment
Penetration testing and security assessments can also help identify vulnerabilities in connected environments before they are exploited.
Prism Infosec provides penetration testing and security assessment services that help organisations identify vulnerabilities across traditional IT infrastructure, cloud platforms and connected devices.
If your organisation is deploying connected technologies or expanding its IoT footprint, security testing can help ensure these systems do not introduce new risks to your network.
Learn more about Prism Infosec’s operational technology security testing services:
Operational Technology Security Testing – Prism Infosec