Strategic Cyber Incident Exercises: Preparing Leadership for the Moments That Matter
Most organisations have an incident response plan, but not all have tested how that plan would perform during a major cyber crisis. Recent cyber incidents continue to demonstrate that technical defences alone are not sufficient. When an organisation experiences a significant breach or ransomware attack, the challenge quickly becomes organisational as opposed to purely technical. […]
Penetration Testing vs GRC: Why Organisations Need Both to Manage Modern Cyber Risk
In many organisations, cybersecurity investment tends to follow one of two directions. Some focus heavily on governance, risk and compliance (GRC) activities such as policies, frameworks and risk registers. Others prioritise technical testing, including penetration testing and red teaming. In practice, both disciplines are essential. Recent industry reporting continues to highlight a growing volume of […]
From Vulnerability Discovery to Effective Remediation

Identifying vulnerabilities is only the first step in improving an organisation’s security posture. Many organisations discover that after a penetration test, audit or vulnerability assessment they are left with a significant list of technical findings but limited internal capacity to address them. In practice, remediation can be complex. Security issues often involve configuration changes, system […]
Ransomware in 2026: Why Extortion Tactics Are Evolving

Ransomware continues to represent one of the most disruptive cyber threats facing organisations. While the techniques used by attackers are evolving, the operational impact remains the same: service disruption, financial loss and reputational damage. If we look to the wider picture, threat intelligence is also indicating to us that ransomware activity is continuing to increase […]
CVE-2026-24061: Critical Telnet Vulnerability Highlights the Ongoing Risk of Legacy Protocols
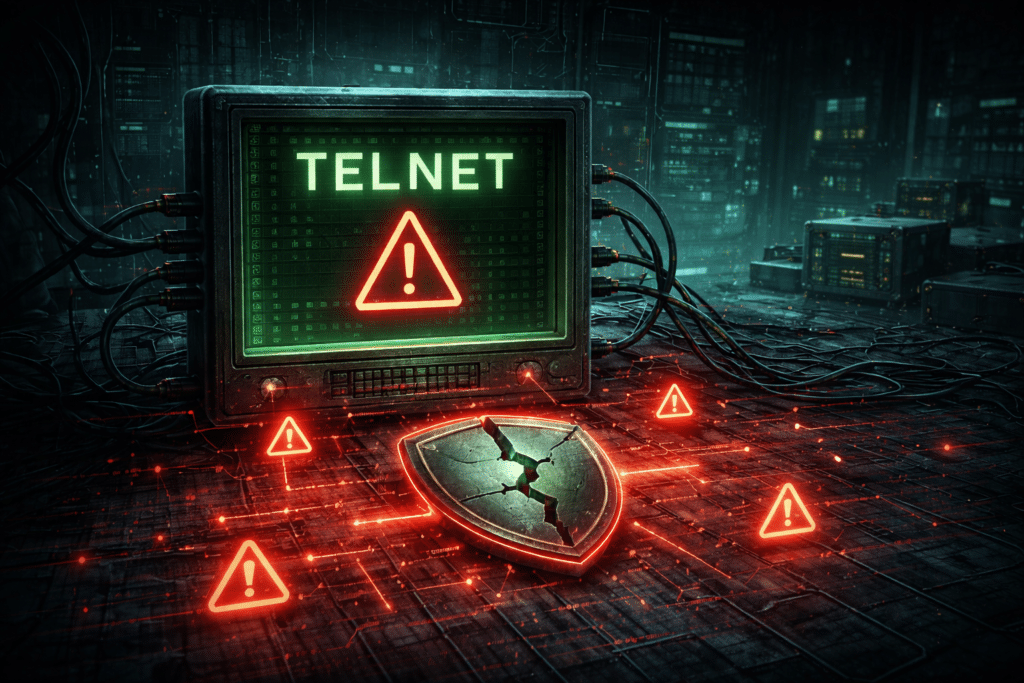
Prism Infosec have been following the recent disclosure of a critical Telnet vulnerability affecting the GNU InetUtils Telnetd server, which has refocused attention widely on the risks posed by legacy protocols that continue to exist within modern IT Infrastructure. Tracked as CVE-2026-24061, the raised flaw allows an unauthenticated attacker the ability to gain root-level access […]
Exploiting Mobile Apps Using Frida
This post explores how the Frida dynamic instrumentation toolkit can be used to bypass common mobile app security controls on both Android and iOS. Using real-world testing examples, it demonstrates how root detection, in-app scoring, and premium content restrictions can be manipulated when protections rely too heavily on client-side logic. The findings highlight the importance of enforcing access control and validation on the server to prevent exploitation.
Beyond Compliance: Building True Cyber Resilience in 2025
Compliance is not enough Across the UK, organisations continue to invest heavily in compliance. ISO 27001 certification, NCSC alignment and annual penetration tests all play an important role. But compliance alone does not guarantee readiness. Compliance demonstrates that controls are in place. Resilience proves they actually work under pressure. Recent incidents have shown that even […]
Securing the Cloud: Visibility, Control and Confidence
Cloud adoption without compromise Cloud platforms have transformed how global organisations deliver services, manage data and scale operations. However, whilst flexibility and speed have improved, visibility and control have often decreased. Many incidents reported to the NCSC over the past year have been linked to cloud misconfiguration or weak access controls, not platform flaws. The […]
Cyber Governance at the Board Level: Turning Awareness into Action
Cyber security is now a boardroom issue In today’s regulatory and operational landscape, cyber security has moved beyond IT. Boards are accountable for the resilience of the business, not just its financial performance. A single cyber incident can disrupt operations, damage reputation and trigger regulatory scrutiny. Awareness is improving, but awareness alone? It’s not enough. […]
From Simulation to Response: Turning Exercises into Real Capability
Running a cyber incident exercise is an excellent way to test response readiness, but too many stop at the simulation itself. The real value lies in what happens afterwards. Every drill, tabletop or technical run-through should end with clear evidence of progress, not a list that disappears into an inbox. Why most exercises fall short […]